A) 802.11a
B) 802.11ac
C) 802.11g
D) 802.11n
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What is one difference between captive portal authentication and 802.1X authentication?
A) 802.1X authentication always authenticates the wireless client, while captive portal authentication always authenticates the wireless user.
B) 802.1X authentication is typically implemented without encryption, while captive authentication is often combined with WPA or WPA2.
C) 802.1X authentication occurs at Layer 2, while captive portal authentication occurs at Layer 3.
D) 802.1X authentication must use an LDAP server, while captive portal authentication can use a RADIUS server or an LDAP server.
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company has an Aruba Mobility Master (MM) -based solution. Where can a network administrator look to find a list of alerts about a variety of issues on the MM or managed devices?
A) the top banner
B) the MM Maintenance pages
C) the Performance dashboard
D) the Potential issues dashboard
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Assume that administrators accept the default forwarding mode for WLANs. How does wireless user traffic flow in a master-local architecture, and how does it flow in a Mobility Master (MM) architecture?
A) In the master-local architecture, traffic is tunneled to a local Mobility Controller (MC) to handle. In a MM architecture, all traffic is tunneled to the MM to handle.
B) In the master-local architecture, all traffic is tunneled to the master controller to handle. In a MM architecture, all traffic is tunneled to the MM to handle.
C) In both architectures, traffic is tunneled to a Mobility Controller (MC) to handle.
D) In both architectures, APs forward corporate user traffic locally and tunnel guest user traffic to a Mobility Controller (MC) to handle.
F) B) and D)
Correct Answer

verified
C
Correct Answer
verified
Multiple Choice
An organization has decided to implement dual SSID Onboarding. An administrator has used the Onboard service template to create services for dual SSID Onboarding. Which statement is true?
A) The Onboard Authorization service is triggered when the user connects to the secure SSID.
B) The Onboard Authorization service is triggered during the Onboarding process.
C) The Onboard Authorization service is never triggered.
D) The device connects to the secure SSID for provisioning.
E) The Onboard Provisioning service is triggered when the user connects to the provisioning SSID to Onboard their device.
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A network administrator examines a list of 2.4GHz clients with low performance in the Mobility Master (MM) dashboard. Which property should pose a concern as a potential performance issue?
A) Radio PHY of HT 20MHz
B) Goodput data rate of 12Mbps
C) Max speed of 72Mbps
D) Usage of 10 MB
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A WLAN in an Aruba Mobility Master (MM) -based solution uses WPA2-Enterprise security. This WLAN currently authenticates users to Active Directory (AD) , and users log in with their Windows domain credentials. Network administrators now want to authenticate the Windows clients as well, based on the client Computer Names. What should the administrator do on MM to achieve this goal?
A) Set up MAC Authentication on the WLAN.
B) Set up Machine Authentication on the WLAN.
C) Import the computer names from AD to the MM internal database.
D) Bind individual Mobility Controllers (MCs) to AD at the device level.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibits. Exhibit 1 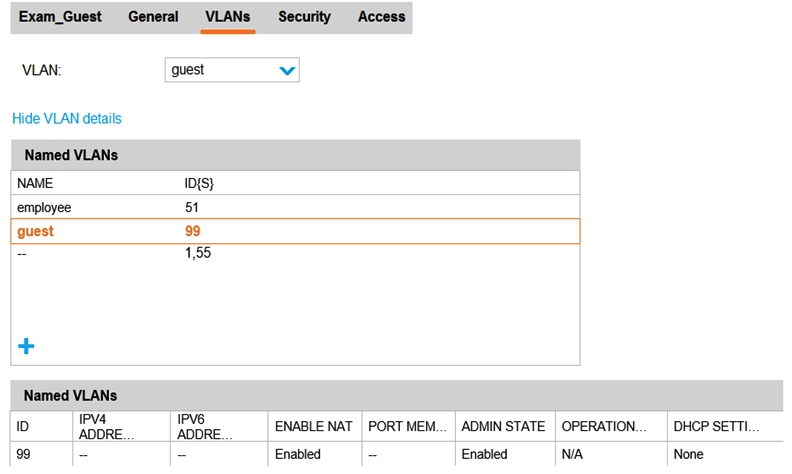 Exhibit 2
Exhibit 2 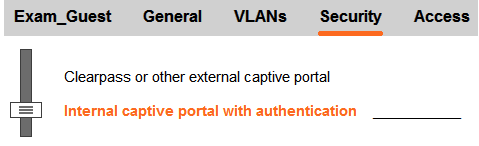 Exhibit 3
Exhibit 3 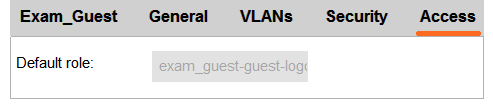 A network administrator creates a guest WLAN on an Aruba Mobility Manager (MM) . The exhibits show some of the settings for the WLAN. The administrator does not change the policies for those roles. How does the firewall control guest clients when they first connect to the WLAN?
A network administrator creates a guest WLAN on an Aruba Mobility Manager (MM) . The exhibits show some of the settings for the WLAN. The administrator does not change the policies for those roles. How does the firewall control guest clients when they first connect to the WLAN?
A) It permits them to send any DHCP traffic and DNS and web traffic to the Internet. It redirects web traffic destined to the private network to a login portal.
B) It does not permit them to send any traffic until they are authenticated.
C) It permits them to send any DHCP and DNS traffic, and it redirects all web traffic to a login portal.
D) It permits them to send any DHCP and RADIUS traffic. It redirects all web traffic destined to the Internet to a login portal and drops web traffic destined to the private network.
F) C) and D)
Correct Answer

verified
C
Correct Answer
verified
Multiple Choice
A company has a Mobility Master (MM) -based solution. A network administrator wants to monitor the types of applications in use in the wireless network. Which dashboard page in the MM interface should the administrator visit?
A) Performance
B) Network
C) Traffic Analysis
D) Security
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 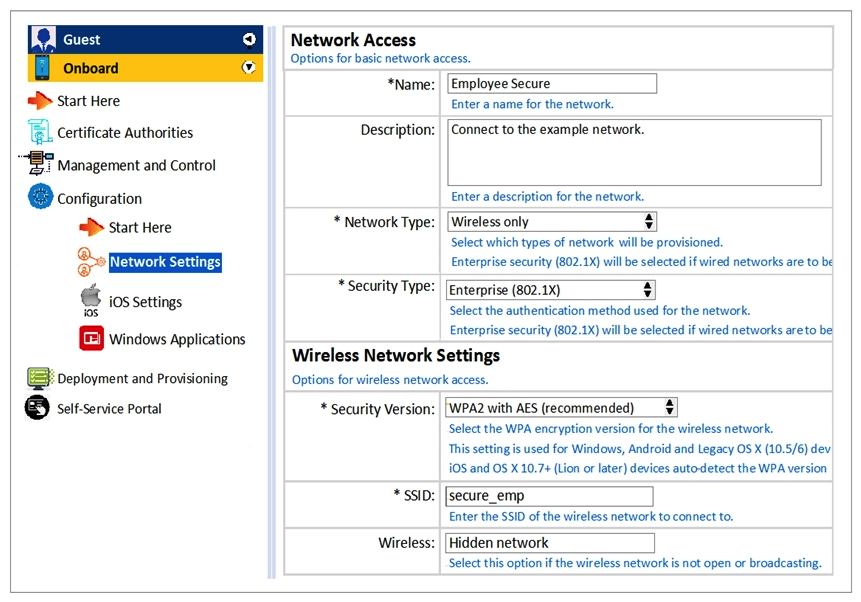 Which statements accurately describe the status of the Onboarded devices in the configuration for the network settings shown? (Choose two.)
Which statements accurately describe the status of the Onboarded devices in the configuration for the network settings shown? (Choose two.)
A) They will use WPA2-PSK with AES when connecting to the SSID.
B) They will to Employee_Secure SSID for provisioning their devices.
C) They will to Employee_Secure SSID after provisioning.
D) They will perform 802.1 authentication when connecting to the SSID.
E) They will connect to secure_emp SSID after provisioning.
G) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A network administrator wants to assign an authentication server group to the WPA2-Enterprise WLAN. Which profile should the administrator modify?
A) Virtual AP
B) SSID
C) AAA
D) L2 Authentication
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Why can't the Onguard posture check be done during 802.1x authentication?
A) Onguard uses TACACS so an additional service must be created.
B) 802.1x is already secure so Onguard is not needed.
C) Health Checks can't be used with 802.1x.
D) Onguard uses RADIUS so an additional service must be created.
E) Onguard uses HTTPS so an additional service must be created.
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What does an Aruba Mobility Master (MM) do before it deploys a configuration to a Mobility Controller (MC) ?
A) It synchronizes the configuration with templates on Aruba AirWave.
B) It removes any commands that are not supported on that MC or have dependency errors.
C) It obtains the current configuration, encrypts it, and backs it up to a secure archive.
D) It encrypts the configuration to be deployed and backs it up to a secure archive.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
How can network administrators upgrade AirMatch on an Aruba Mobility Master (MM) ?
A) Upgrade Client Match as part of a global software upgrade, and upgrade AirMatch separately as a loadable service module (LSM) .
B) Upgrade Client Match and AirMatch separately as loadable service modules (LSMs) .
C) Upgrade AirMatch and Client Match through a global software upgrade.
D) Upgrade AirMatch as part of a global software upgrade, and upgrade Client Match separately as a loadable service module (LSM) .
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An AP operates on channel 6. Which device causes the most significant and consistent interference with the signal?
A) cellular phone
B) AP operating on channel 11
C) wireless security camera operating on channel 8
D) weather radar
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What is a key difference between an Aruba Air Monitor (AM) and an Aruba Spectrum Analyzer (SA) ?
A) An AM detects threats such as rogue APs, while an SA analyzes RF conditions.
B) An AM detects rogue APs and provides data services to clients, while an SA only detects rogue APs.
C) An AM scans on only one 802.11 frequency band, while an SA scans on both 802.11 frequency bands.
D) An AM both detects wireless intrusion attempts and mitigates them, while an SA only detects wireless intrusion attempts.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 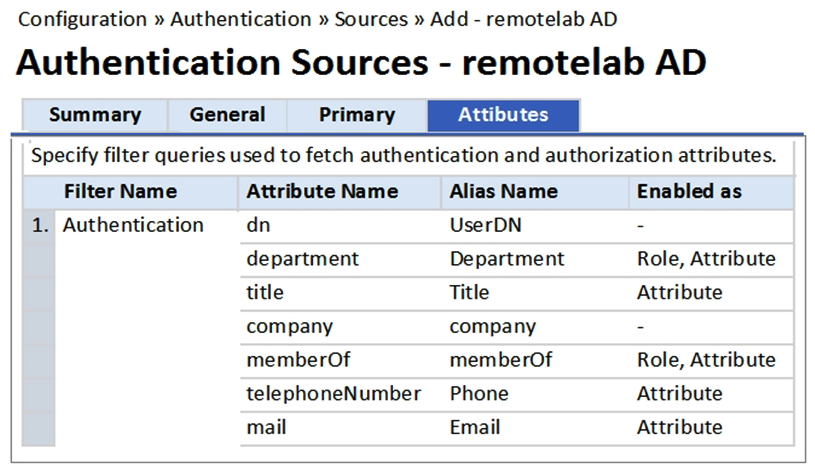 Based on the Attribute configuration shown, which statement accurately describes the status of attribute values?
Based on the Attribute configuration shown, which statement accurately describes the status of attribute values?
A) The attribute values of department, title, memberOf, telephoneNumber, mail are directly applied as ClearPass roles.
B) The attribute values of department and memberOf are directly applied as ClearPass roles.
C) Only the attribute value of company can be used in role mapping policies, not other attributes.
D) Only the attribute value of department and memberOf can be used in role mapping policies.
E) Only the attribute value of title, memberOf, telephoneNumber can be used in role mapping policies.
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which components of a ClearPass is mandatory?
A) Authorization Source
B) Enforcement
C) Profiler
D) Role Mapping Policy
E) Posture
G) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
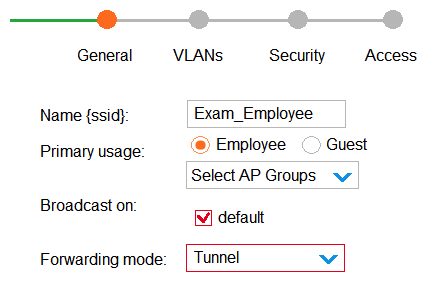 What describes the behavior for this WLAN?
What describes the behavior for this WLAN?
A) No APs broadcast the SSID. Clients cannot connect to the WLAN until administrators activate it.
B) APs in the default group broadcast the SSID. Clients can connect to the WLAN on APs in any group.
C) No APs broadcast the SSID. Clients can connect to the WLAN on APs in the default group only.
D) APs in the default group broadcast the SSID. Clients can connect to the WLAN on APs in the default group only.
F) All of the above
Correct Answer

verified
C
Correct Answer
verified
Multiple Choice
A company has an Aruba Mobility Master (MM) -based solution. Under which circumstance will an AP radio change channel without the use of the Mobility Master (MM) ?
A) when the MM detects that a different channel has significant better quality
B) when the AP detects a large amount of interference on its channel
C) when the Mobility Controller (MC) detects a rogue AP on the channel
D) when the Client Match rules indicate that nearby clients do not support the current channel
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Showing 1 - 20 of 40
Related Exams